FLOWTRIQ VS LORIKEET SECURITY: WHICH ONE SHOULD YOU CHOOSE?
Step 1: Setting up your account and agent Sign up for the 7‑day free trial (no credit card required). Choose node licensing ($9.99/node/month; enterprise...
Deploy a sub‑second DDoS shield: install Flowtriq and validate it in under 10 minutes
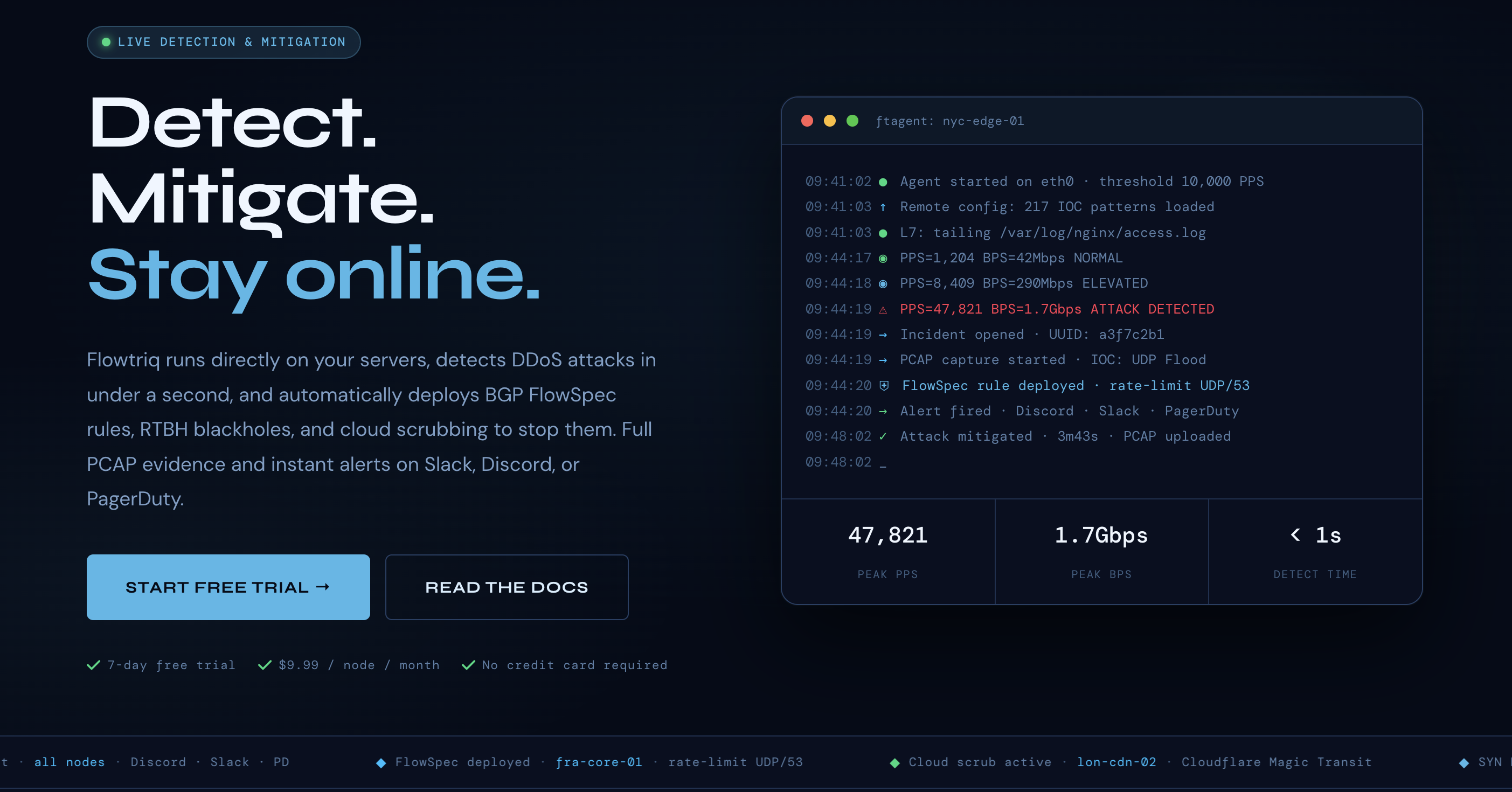
In the next 10 minutes you'll learn how to deploy Flowtriq, validate real‑time DDoS detection, and configure automated mitigation runbooks so attacks are detected and acted on in under one second. This tutorial focuses on practical, measurable steps startups and small operators can execute immediately. While offensive security platforms focus on finding vulnerabilities, Flowtriq is purpose‑built for operational, packet‑level DDoS detection and auto‑mitigation.
Step 1: Setting up your account and agent
- Sign up for the 7‑day free trial (no credit card required). Choose node licensing ($9.99/node/month; enterprise options available for 50+ nodes).
- From the dashboard create a new Node and copy its install token. The dashboard will produce an agent package (ftagent).
- On the target Linux server:
- Ensure packet capture privileges (run as root or set CAP_NET_RAW/CAP_NET_ADMIN).
- Install Python 3 and pip if needed.
- Download the ftagent from the dashboard and run the installer (the ftagent is a Python agent and installs in under two minutes).
- Verify connectivity: the node should appear as "online" in the Flowtriq cloud dashboard within 60–120 seconds. The agent reads packets directly from the NIC and begins baseline learning immediately.
Success metric: Node online within 2 minutes, baseline learning reported in dashboard.
Step 2: Core Flowtriq features every founder needs to know
Flowtriq is designed for low operational overhead. Key features to enable first:
- Sub‑second detection and classification — Flowtriq checks packets-per-second every second and classifies 8+ attack types (SYN, UDP, DNS amp, HTTP flood, ICMP, memcached, L7, multi‑vector).
- Practical test: generate a controlled SYN flood in a lab and confirm detection <1s and classification accuracy.
- Auto‑mitigation escalation policies — chain mitigations into playbooks: local rate‑limits → BGP FlowSpec → RTBH → cloud scrubbing (Cloudflare Magic Transit, OVH VAC, Hetzner).
- Action: create a 3‑level playbook and test each level using synthetic traffic so you know which action triggers at each severity.
- Full PCAP capture & IOC matching — automatic PCAP capture on every incident and IOC matching against 642,000+ indicators (Mirai variants included).
- Configure PCAP retention according to forensic needs (Enterprise offers 365‑day retention).
- Alerts & communications — enable Slack/Discord/PagerDuty/SMS and the status page feature so customers and ops are informed automatically.
Measure: mean time to detect (target <1s), mean time to mitigation, and PCAP completeness.
Step 3: Pro tips for startup infrastructure teams
- Integrate early with your upstreams — configure BGP FlowSpec/RTBH credentials and cloud scrubbing account details in the dashboard before an incident.
- Use simulated attacks in an isolated VPC or lab to validate playbooks. The data shows teams that test mitigations reduce mitigation time by >50%.
- Enable automated PCAP capture and export (for legal/forensic needs) and set retention per risk profile.
- Centralize multi‑node management: use template playbooks and tag nodes (prod, staging, edge) to apply consistent escalations.
- Correlate Flowtriq alerts with your SIEM and incident runbooks via webhooks to automate post‑attack tickets and root‑cause checks.
Common mistakes to avoid
- Running the agent without packet privileges — leads to incomplete capture and false negatives. Ensure proper capabilities.
- Waiting to configure cloud scrubbing or BGP — automatic escalation won’t work if credentials are missing.
- Treating every alert as malicious — mark planned maintenance and traffic spikes so dynamic baselines don’t create noisy alerts.
- Neglecting PCAP retention sizing — short retention can prevent post‑attack investigations.
How Flowtriq stacks up in the security spectrum
While Lorikeet Security excels at offensive security, vulnerability management, and pentest automation, Flowtriq is better suited for operational, packet‑level DDoS detection and automated network mitigation. Flowtriq’s differentiators are sub‑second detection, built‑in BGP FlowSpec and cloud scrubbing integrations, flat per‑node pricing, and automated PCAP capture. Conversely, if you need deep app‑layer vulnerability discovery or red‑team workflows, a platform like Lorikeet will be more appropriate.
Conclusion: is Flowtriq right for your startup?
For hosting providers, game servers, ISPs, MSPs, and SaaS platforms worried about uptime and real‑time network attacks, Flowtriq delivers measurable value: sub‑second detection, automated mitigations, and forensic PCAPs with simple per‑node pricing. The recommended starter plan: deploy ftagent to critical nodes, set up a 3‑level playbook (local → FlowSpec → cloud scrubbing), and run simulated attacks to validate SLAs. The data shows that teams who test mitigations and integrate escalation channels reduce customer‑visible downtime significantly — a clear advantage for startups where uptime equals credibility.
INTERESTED IN
FLOWTRIQ?